Security
Keeping your data and systems protected is crucial to the success and safety of your business in this digital age.
We partner with security vendors to bring you the best protection
Cyberattacks come in all shapes and sizes. They are frequent, well disguised and can be deadly to your business if you are not prepared.
In fact, a recent report stated that cybercriminals launch attacks every 39 seconds, which is an average of 2,244 times per day.
So, how would your business fare if you came under an attack?
Do you have the defences in place to keep the cybercriminals out or would you essentially be handing them the keys to your business, confidential data and bank accounts?
Sadly, this is the reality of operating a business in this digital age. The benefits are plentiful, but the risks can be critical if you don’t get the best protection in place.
How do we secure your businesses' data and systems?
At Affinity, we are a Gold ESET UK Partner which allows to implement the best possible protection available on the market.
Here’s how we minimise security risks to your business:
Enhanced spam filtering
Our spam filters reduce the human risk of clicking links and attachments that can we harmful to your business. One wrong click could compromise your whole business and unlock the door to a cybercriminal!
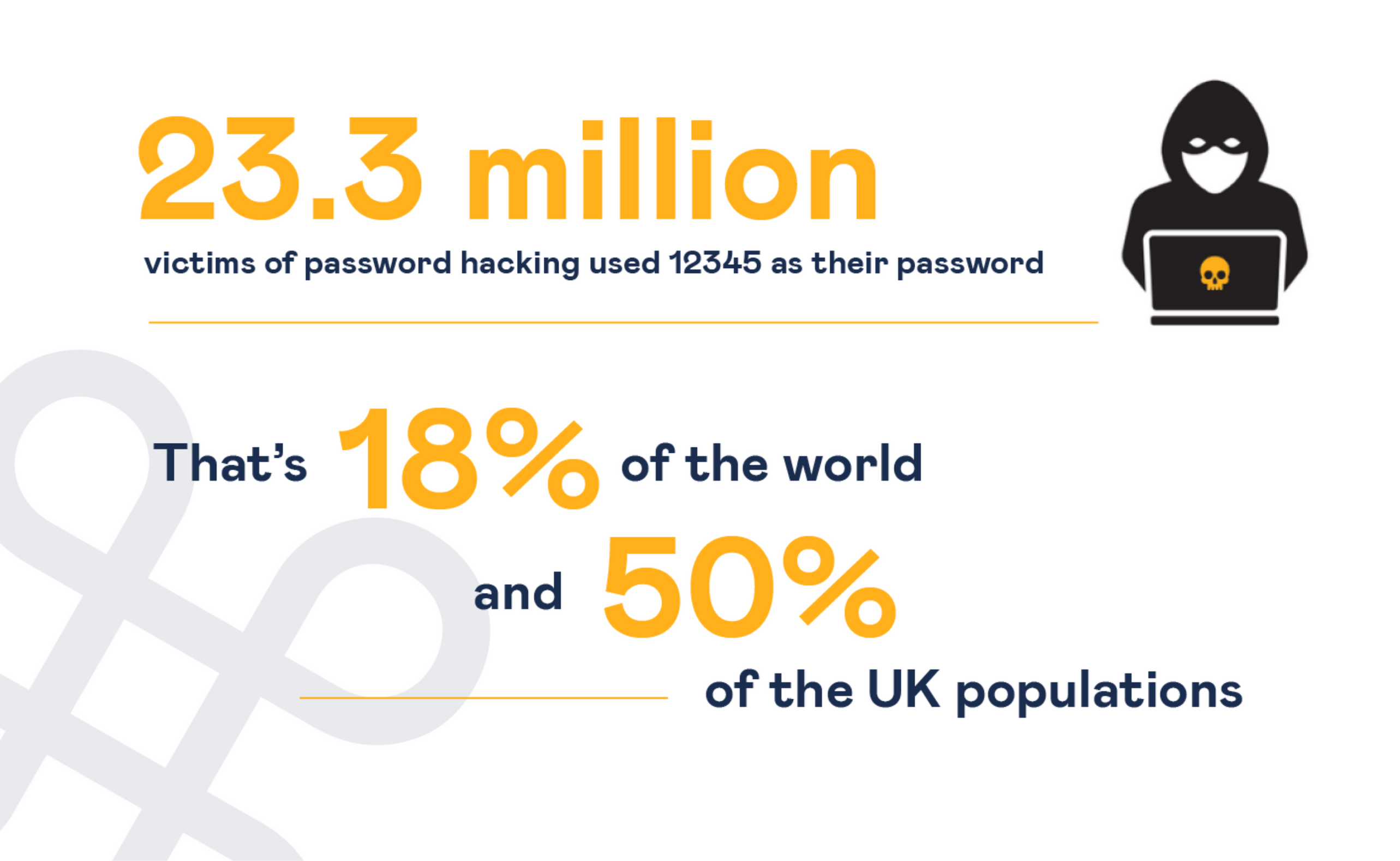
Password management systems
Are your passwords complex enough? Do you use the same password for your PC as your do your bank account? Poor password hygiene is one of the easiest routes in for a cybercriminal but can be easily offset by using a management system which flags weak and recurring passwords for added protection.
In-depth system monitoring
By monitoring your systems daily, we are able to spot any irregular activity on your accounts, target them immediately and make sure that attacks don’t become business critical.
Antivirus and encryption for your all desktops, laptops, phones and tablets
Any device that is used to access your businesses’ data and systems could potentially be a way in for a cybercriminal. This additional layer of protection will make sure that none of your employees’ devices could be considered a weak spot.
Our 24/7 Dark Web Monitoring solution, powered by Dark Web ID, provides you critical alerts should your business domain or employee credentials be discovered on the Dark Web.
Not sure what protection you already have?
Book a FREE review of your IT infrastructure and IT Security TODAY!
We can’t recommend a review of your IT security enough.
Our reviews will check around 100 elements of your setup to give you complete visibility, practical solutions and hopefully peace of mind.
If you don’t know what you’re doing to keep your businesses’ data and systems protected, or are concerned that you might not have any protection in place whatsoever, please do not hesitate in contacting Affinity today.
Click here to book your review
Request more information on Security
Key Services
Related IT Services
-

Free Remote Working Review
Are You Remote Working Ready?
Free review to assess if you are ready for remote working.
Call us on 0114 362 7000 or click here for a callback.Read more…
-
Dark Web Monitoring
Hackers and cybercriminals launch attacks every 39 seconds, which is an average of 2,244 times per day, with more than 8 Billion records confirmed to be compromised in the last year alone.
-
Security Awareness Training and Phishing Simulations
Can your employees spot a cleverly disguised email phishing attack hiding in their inbox?
-
Managed IT Support